Last updated on March 17, 2026
Google Cloud Hybrid Connectivity Cheat Sheet
- There are several ways to extend your on-premises environment to the Google Cloud Platform.
- You can connect your infrastructure to Google Cloud Platform (GCP) on your terms, from anywhere based on your requirements.
Cloud Interconnect
- Provides low latency, highly available connections that enable you to reliably transfer data between your on-premises and Google Cloud VPCs.
- Cloud Interconnect connections provide internal IP address communication, which means internal IP addresses are directly accessible from both networks.
- Cloud Interconnect offers two options to extend your on-premises network to the Google Cloud Platform:
- Dedicated Interconnect
- Direct physical Connection to Google’s network.
- Partner Interconnect
- Provides connectivity through a supported service provider.
- You can use Cloud Interconnect in combination with Private Google Access for on-premises resources so that your on-premises resources can use internal IP addresses rather than external IP addresses to reach Google APIs and services.
- Cross-Cloud Interconnect: Direct connection to AWS, Azure, and Oracle Cloud. Managed service with high bandwidth.
- Cross-Site Interconnect: Connect your on-premises sites to each other through Google’s network.
- Resiliency and SLA options:
- Critical production: 99.99% uptime SLA
- Non-critical production: 99.9% uptime SLA
- No SLA option available
- Encryption options:
- MACsec for Cloud Interconnect: Encrypt traffic between on-premises router and Google’s edge routers
- HA VPN over Interconnect: Add IPsec encryption to Interconnect traffic
- MTU support: VLAN attachments support 1440, 1460, 1500, and 8896 bytes; cross-site networks support 9000 bytes.
- Custom IP address ranges: Configure specific IPs for Cloud Router and customer router ends of VLAN attachments (/29 or /30 for IPv4, /125 or /126 for IPv6).
- Application awareness: Map outbound traffic to different classes using DSCP for traffic prioritization (business-critical vs lower priority).
- Network Topology visualization: View Interconnect connections and VLAN attachments in Network Topology tool.
- GRE traffic support: Terminate GRE traffic on VMs from Interconnect connections (GRE version 0 only).
- Dedicated Interconnect
Direct Peering
- Direct Peering connects your on-premises network to Google services, including Google Cloud products that can be exposed via one or more public IP addresses.
- Traffic from Google’s network to your on-premises network also takes that same connection, including traffic from VPC networks in your projects.
- Direct Peering exists outside of Google Cloud Platform. So, unless you need to access Google Workspace applications, the recommended methods of access to Google Cloud Platform are via Dedicated Interconnect or Partner Interconnect.
Carrier Peering
- Carrier Peering enables you to access Google applications, such as Google Workspace, by using a service provider to obtain enterprise-grade network services that connect your infrastructure to Google.
- When connecting to Google through a service provider, you can get connections with higher availability and lower latency, using one or more links.
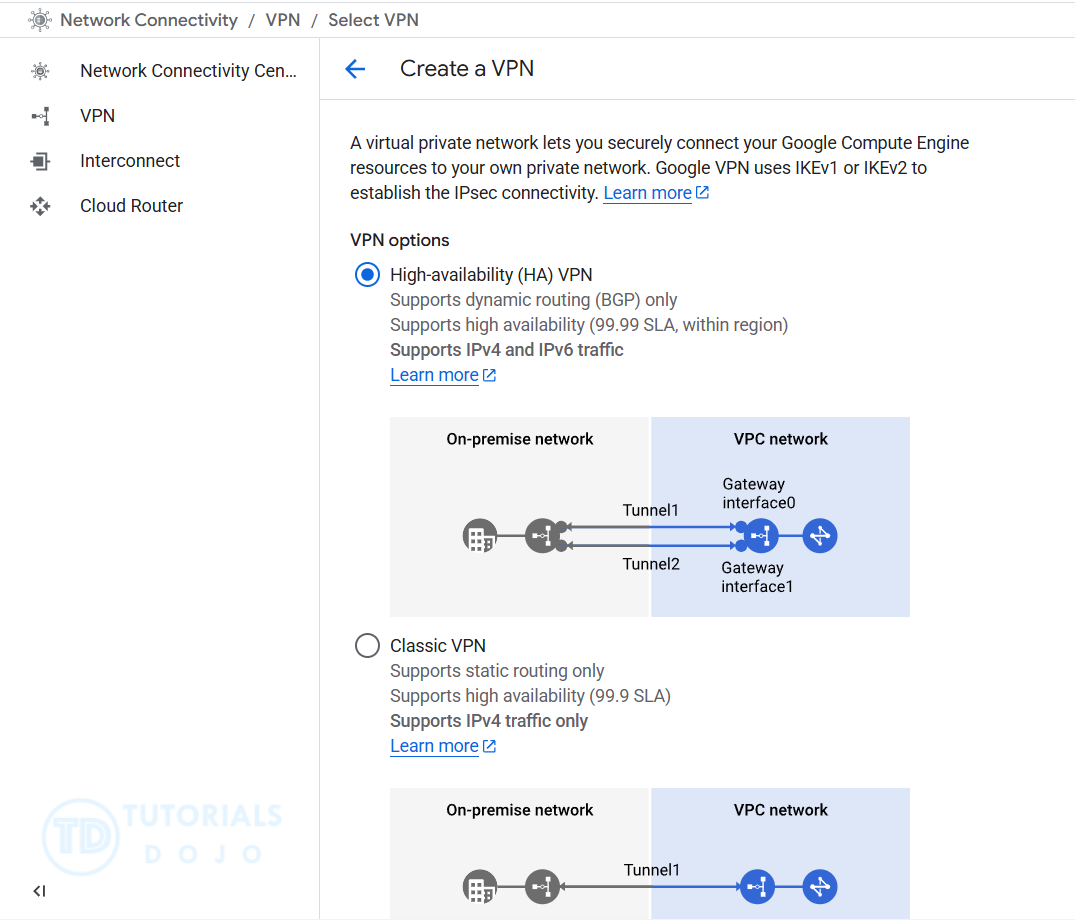
Cloud VPN
- HA VPN (High Availability):
- 99.99% SLA (99.9% for some topologies)
- Dynamic routing only (BGP)
- Two external IP addresses automatically assigned
- Supports IPv6 (dual-stack and IPv6-only configurations)
- Supports up to 250,000 packets per second per tunnel (1–3 Gbps)
- Classic VPN:
- 99.9% SLA
- Static routing (policy-based or route-based)
- Single external IP address
- IPv4 only
- HA VPN over Cloud Interconnect: Add IPsec encryption to Interconnect traffic for regulatory compliance.
- Bandwidth: Each tunnel supports up to 250,000 packets per second (combined ingress/egress). Equivalent to 1–3 Gbps depending on packet size.
- IPv6 support: Available only in HA VPN. Use IPV6_ONLY or IPV4_IPV6 stack types.
- IKE support: IKEv1 and IKEv2 with pre-shared keys. Cipher configuration available for IKEv2 (AEAD and non-AEAD ciphers).
- GRE traffic support: Terminate GRE traffic on VMs from VPN tunnels (GRE version 0 only).
- Network Topology visualization: View VPN gateways and tunnels in Network Topology tool.
- Dead Peer Detection (DPD): Automatically detects unhealthy tunnels and fails over traffic.
- Bring Your Own IP (BYOIP): Use your own public IP addresses with Cloud VPN.
- Restrict peer IPs: Organization policy to restrict which peer IP addresses can be used for VPN tunnels.
Network Connectivity Center
- Hub-and-spoke model to connect multiple on-premises sites and VPC networks using Google’s network as a WAN.
- Spoke types: VPN tunnels, VLAN attachments, and router appliance instances.
- Reduces complexity of managing multiple point-to-point connections.
- Traffic between sites stays on Google’s private backbone.
Pricing
Cloud Hybrid Connectivity pricing varies by service and usage:
- Cloud Interconnect: Charges apply for connections (Dedicated, Partner, Cross-Cloud, Cross-Site) based on capacity and location.
- Cloud VPN: Charges apply per VPN gateway, per tunnel, and for data transfer.
- Network Connectivity Center: Charges apply for hub processing and spoke attachments.
- Data Transfer: Egress charges vary by destination and network tier (Premium vs Standard).
For current pricing details, refer to the official Google Cloud pricing pages for each connectivity service.
Validate Your Knowledge
Question 1
You are running VMs that are currently reaching the maximum capacity on your on-premises data center. You decided to extend your data center infrastructure to Google Cloud to accommodate new workloads. You have to ensure that the VMs that you provisioned in GCP can communicate directly with on-premises resources via a private IP range.
What should you do?
- Create a VPC on Google Cloud and configure it as a host for a Shared VPC.
- Build a custom-mode VPC. Set up VPC Network Peering between your on-premises network and your newly created VPC to establish a connection through a private IP range.
- Provision virtual machines on your on-premises and Google Cloud VPC networks that will serve as bastion hosts. Configure the VMs as proxy servers using public IP addresses.
- Set up Cloud VPN between your on-premises network to a VPC network through an IPsec VPN connection.
For more Google Cloud practice exam questions with detailed explanations, check out the Tutorials Dojo Portal:
Google Cloud Hybrid Connectivity Cheat Sheet References:
https://cloud.google.com/hybrid-connectivity
https://cloud.google.com/network-connectivity/docs/interconnect/concepts/overview
https://cloud.google.com/network-connectivity/docs/vpn/concepts/overview
https://cloud.google.com/network-connectivity/docs/direct-peering