Last updated on January 8, 2026
Azure Firewall Cheat Sheet
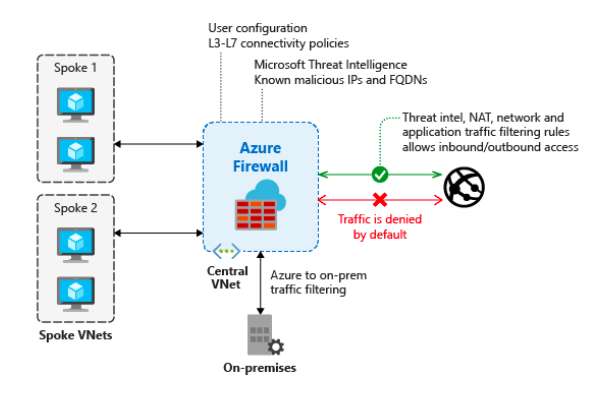
- A cloud-native, intelligent network firewall security service that protects Azure cloud workloads. It is available in three service tiers (SKUs) to meet different needs: Basic, Standard, and Premium.
- Azure Firewall is PCI, SOC, ISO, ICSA Labs, and HITRUST compliant.
Features
- Service Tiers (SKUs)
- Azure Firewall Basic: Designed for SMBs. Provides essential protection with a fixed scale unit and a recommended throughput of up to 250 Mbps. Supports Threat Intelligence in alert mode only.
- Azure Firewall Standard: Offers L3-L7 filtering and real-time Threat Intelligence that can alert and block traffic to/from known malicious IPs and domains.
- Azure Firewall Premium: Includes all Standard features and adds advanced Signature-based Intrusion Detection and Prevention System (IDPS). It uses a database of over 67,000 signatures across 50+ categories (e.g., malware, phishing) to detect and stop rapid attacks.
- Management & Governance:
- Centralized Management with Firewall Policies: Azure Firewall Manager allows central management of multiple firewalls across subscriptions. It uses firewall policies to apply a common set of network/application rules and configurations.
- A stateful firewall service.
- You can enable forced tunneling to route Internet-bound traffic to an additional firewall or virtual network appliance.
- Limit outbound traffic to a given FQDN list, including wild cards.
- Filter any TCP/UDP protocol outbound traffic.
- To use FQDNs in your rules, you must enable DNS proxy.
- Deny the traffic of a malicious IP address with threat intelligence-based filtering.
- It has the highest priority rules and will always be processed first.
- Threat intelligence (supported in Standard and Premium tiers): Modes include Alert only and Alert and deny to block traffic from known malicious IPs/domains. The Basic SKU supports Alert mode only.
- With a DNS proxy, a firewall listens to port 53 and forwards the DNS requests to a DNS server.
- You can minimize the complexity of creating a security rule using a service tag.
- Associate up to 250 public IP addresses in your firewall (Premium SKU feature).
- It supports SNAT and DNAT translation.
- SNAT – Source NAT for outbound VNet traffic.
- DNAT – Destination NAT for inbound network traffic.
- Azure Firewall diagnostic logs (JSON format):
- Application rule log
- Network rule log
- You can store all your logs in a storage account, event hubs, and Azure monitor logs.
- Azure Firewall metrics:
- Application/Network rules hit count
- Data processed
- Throughput
- Firewall health state
- SNAT port utilization
- To manage multiple firewalls, you can use Azure Firewall Manager.
- Protect your VDI deployments using Azure firewall DNAT rules and threat Intelligence filtering.
Azure Firewall Pricing
- Pricing is based on the selected SKU (Basic, Standard, Premium), deployment hours, and data processed. Each SKU has a different compute cost per hour. Review the Azure Firewall pricing page for detailed rates.
Validate Your Knowledge
Question 1
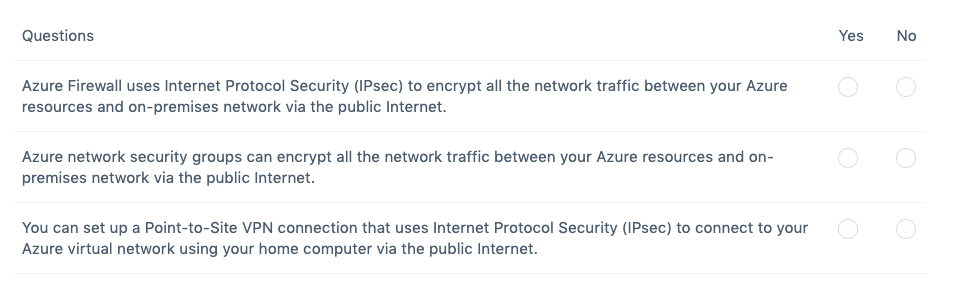
Question Type: Hotspot
For each of the following items, choose Yes if the statement is true or choose No if the statement is false. Take note that each correct item is worth one point.
For more Azure practice exam questions with detailed explanations, check out the Tutorials Dojo Portal:
Azure Firewall Cheat Sheet References:
https://azure.microsoft.com/en-us/services/azure-firewall/
https://docs.microsoft.com/en-us/azure/firewall/overview