Last updated on March 17, 2026
Google Cloud Router Cheat Sheet
- Cloud Router is a fully distributed and managed Google Cloud service that helps you define custom dynamic routes and scales with your network traffic.
Features
- It works with both legacy networks and Virtual Private Cloud (VPC) networks.
- Cloud Router utilizes Border Gateway Protocol (BGP) to exchange routes between your Virtual Private Cloud (VPC) network and your on-premises network.
- Supports Bidirectional Forwarding Detection (BFD) for faster failure detection on BGP sessions.
- Supports MD5 authentication for secure BGP session establishment.
- BGP route policies: Set rules to filter BGP routes or modify BGP route attributes.
- Using Cloud Router is required or recommended in the following cases:
- Required for Cloud NAT
- Required for Dedicated Interconnect, Cross-Cloud Interconnect, Partner Interconnect, Router appliances, and HA VPN
- A recommended configuration option for Classic VPN
- When you extend your on-premises network to Google Cloud, use Cloud Router to dynamically exchange routes between your Google Cloud networks and your on-premises network.
- Cloud Router peers with your on-premises VPN gateway or router. The routers exchange topology information through BGP.
Route Advertisements
- Through BGP, Cloud Router advertises the IP addresses of Google resources that clients in your on-premises network can reach. Your on-premises network then sends packets to your VPC network that have a destination IP address matching an advertised IP range. After reaching Google Cloud, your VPC network’s firewall rules and routes determine how Google Cloud route the packets.
- Default Route Advertisement – Cloud Router advertises subnets in its region for regional dynamic routing or all subnets in a VPC network for global dynamic routing.
- Custom Route Advertisement – You explicitly specify the routes that a Cloud Router advertises to your on-premises network.
- IPv6 Support
- Cloud Router supports IPv6 route exchange through either:
- BGP over IPv6
- BGP over IPv4 using multiprotocol BGP (MP-BGP)
- Supported BGP session types:
- IPv4 BGP sessions that exchange only IPv4 prefixes
- IPv6 BGP sessions that exchange only IPv6 prefixes
- IPv4 BGP sessions using MP-BGP that exchange both IPv4 and IPv6 prefixes
- IPv6 BGP sessions using MP-BGP that exchange both IPv4 and IPv6 prefixes
- For HA VPN tunnels or Dedicated Interconnect VLAN attachments, you can configure both an IPv4 BGP session and an IPv6 BGP session simultaneously.
- Limitations – IPv6 BGP peering and IPv6 route exchange are NOT supported for:
- Classic VPN tunnels
- Router appliance instance
- Cross-Cloud Interconnect VLAN attachments
- Cloud Router supports IPv6 route exchange through either:
Pricing
- Cloud Router pricing is based on the number of BGP sessions and the amount of data processed.
- There is no charge for the Cloud Router service itself.
- You incur standard charges for:
- Data transfer through Cloud Interconnect, Cloud VPN, or Network Connectivity Center connections
- Resources managed by Cloud Router (VLAN attachments, VPN tunnels, etc.)
For current pricing details, refer to the official Google Cloud pricing pages for Cloud Interconnect, Cloud VPN, and Network Connectivity Center.
Validate Your Knowledge
Question 1
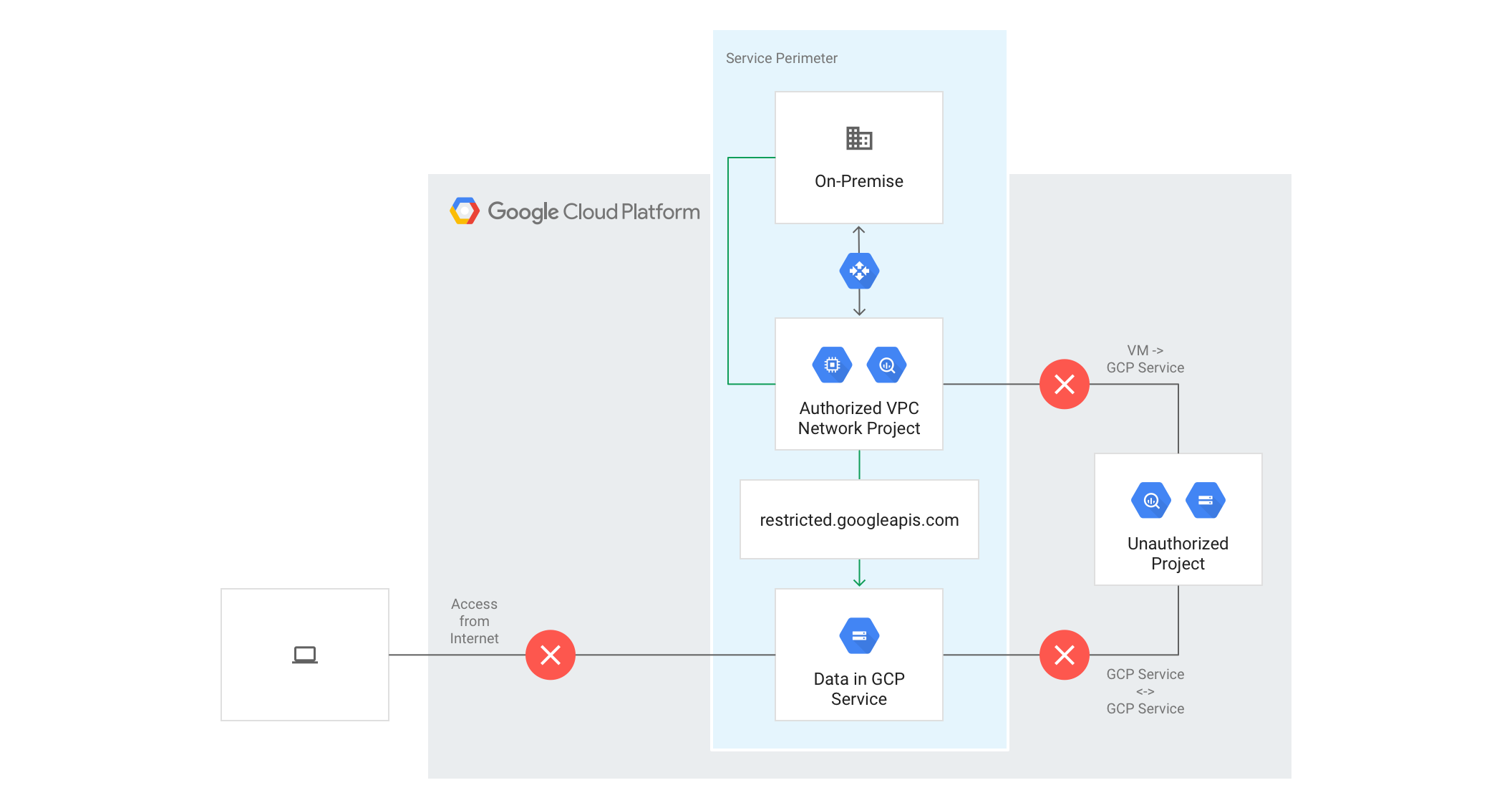
You are hosting a web application in your on-premises data center that needs to fetch files from a Cloud Storage bucket. However, your company strictly implements security policies that prohibit your bare-metal servers from having a public IP address or having any access to the Internet. You want to follow Google-recommended practices to provide your web application the necessary access to Cloud Storage.
What should you do?
-
a. Issue
nslookupcommand on your command-line to get the IP address forstorage.googleapis.com.
b. Discuss with the security team why you need to have a public IP address for the servers.
c. Explicitly allow egress traffic from your servers to the IP address ofstorage.googleapis.com. -
a. Create a VPN tunnel connecting to a custom-mode VPC in the Google Cloud Platform using Cloud VPN.
b. Create a Compute Engine instance and install the Squid Proxy Server. Use the custom-mode VPC as the location.
c. Configure your on-premises servers to use the new instance as a proxy to access the Cloud Storage bucket. -
a. Migrate your on-premises server using
Migrate for Compute Engine(formerly known as Velostrata).
b. Provision an internal load balancer (ILB) that usesstorage.googleapis.comas a backend.
c. Set up the new instances to use the ILB as a proxy to connect to the Cloud Storage. -
a. Create a VPN tunnel to GCP using Cloud VPN or Cloud Interconnect.
b. Use Cloud Router to create a custom route advertisement for199.36.153.4/30. Announce that network to your on-premises network via VPN tunnel.
c. Configure the DNS server in your on-premises network to resolve*.googleapis.comas a CNAME to restricted.googleapis.com.
For more Google Cloud practice exam questions with detailed explanations, check out the Tutorials Dojo Portal:
Google Cloud Router Cheat Sheet Reference:
https://cloud.google.com/network-connectivity/docs/router/concepts/overview