Last updated on July 11, 2024
What is an AWS KMS key?
In security, a KMS key is what you use to encrypt all other encryption keys in your system. KMS key is a logical representation of a cryptographic key. They are the primary resources in AWS KMS. The AWS KMS Key contains the key material used to encrypt and decrypt data. It also contains metadata such as the key ID, creation date, description, and key state.
You can start using AWS KMS through the web console or via API. There are two types of AWS KMS keys that you can create in AWS KMS: symmetric encryption keys and asymmetric keys.
- A symmetric encryption keys is a 256-bit key that is used for standard encryption and decryption.
- An asymmetric keys, on the other hand, is an RSA key pair that is used for encryption and decryption or signing and verification, but not both, or an elliptic curve (ECC) key pair that is used for signing and verification.
Likewise, AWS breaks down KMS key ownership into three categories: customer-managed keys, AWS managed keys, and AWS owned keys. Generally, when you create a KMS key, AWS KMS provides the key material for it; But if you require to have full control of your keys, customer-managed keys allow you to upload your own key material into AWS. The level of control you have varies for each category, with customer-managed keys being the most unrestricted, to AWS owned keys being the most restrictive.
How To Manage Access To Your KMS Key
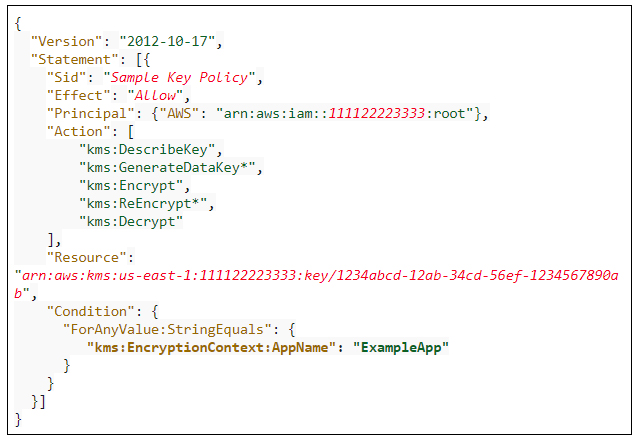
To protect your KMS key from unauthorized access, you must attach a key policy to it. Key policies help protect your KMS key by defining specific requirements that must be fulfilled before an action is permitted. The policy structure is similar to IAM policies, and it also uses JSON formatting. Here is a basic example of a key policy:
To create your key policy, you must first indicate the policy version you will be using. Then in the statement body, you must include the following parameters:
- Effect – indicates whether the policy will allow or deny actions
- Principal – the identity to which the policy will grant or deny permissions to
- Action – the permissions that you want to grant/deny to the principal
- Resource – the list of objects that your policy will be applied to
You can also include the following optional parameters in your statement body:
- Sid – a unique identifier for your policy
- Conditions – conditions that need to be met before your policy takes effect
The AWS KMS documentation has a list of all accepted values for the policy body, along with some examples to guide you through.
The key policy applied to a KMS key created through the AWS KMS API
When you create a KMS key using the API and you do not provide a key policy in the parameters, AWS automatically creates and assigns a default key policy for your KMS key. This default key policy has one policy statement that gives the AWS root account that owns the KMS key full access to the KMS key and enables IAM policies in the account to allow access to the KMS key. If later on, you decide to change the contents of the key policy, you need to create a new policy and attach it to your KMS key to replace the old one.
The key policy applied to a KMS key created through the AWS Management Console
When you create a KMS key with the AWS Management Console, you can choose the IAM users, IAM roles, and AWS accounts that should be given access to the KMS key, and these will be added to a default key policy that the console creates for you. With the console, you can view or modify your key policies. The default key policy gives the AWS root account that owns the KMS key full access to the KMS key. You can also specify in the default key policy which IAM users and roles will be key administrators and key users, which have different respective policy statements.
Note: If you are studying for the AWS Certified Security Specialty exam, we highly recommend that you take our AWS Certified Security – Specialty Practice Exams and read our Security Specialty exam study guide.
Sources:
https://docs.aws.amazon.com/kms/latest/developerguide/concepts.html#master_keys
https://docs.aws.amazon.com/kms/latest/developerguide/key-policies.html
https://docs.aws.amazon.com/kms/latest/developerguide/control-access-overview.html#managing-access