Last updated on February 25, 2025
What is Amazon S3 Glacier Vault Lock
A Glacier Vault can be described as a container for your archived objects in S3 Glacier. To begin using Amazon S3 Glacier, you need a vault. Creating and deleting vaults can be easily done in the AWS Management Console, but interacting with them requires you to use the APIs. For example, let’s say you want to upload images or log files to your vault. To do so, you would either use the AWS CLI or write code that would upload these objects.
Large corporations often have compliance requirements with how they store their data. To meet these requirements, you can use a feature in S3 Glacier called a Vault Lock. S3 Glacier Vault Lock allows you to create a vault lock policy that specifies how your archives will be handled. You can specify controls such as “write once read many” (WORM) in a vault lock policy and lock the policy from future edits. Once locked, the policy can no longer be changed.
You can include a bunch of controls in a vault lock policy, such as data retention based on duration or tags. These policies are written similarly as IAM Policies which follow JSON formatting. You can set one vault lock policy for each vault.
How To Lock Your Glacier Vault Using Glacier API
Vault locking follows a two-step process:
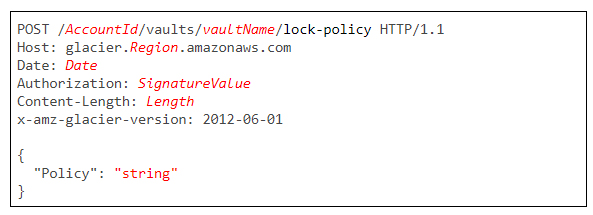
- Initiate the lock by attaching a vault lock policy to your vault, which sets the lock to an in-progress state and returns a lock ID. While in the in-progress state, you have 24 hours to validate your vault lock policy before the lock ID expires.
The API call for this step is a POST request to the URI of your Glacier vault’s lock policy. The request body should contain your intended policy statement.
If your POST request is successful, AWS returns an HTTP 201 response.
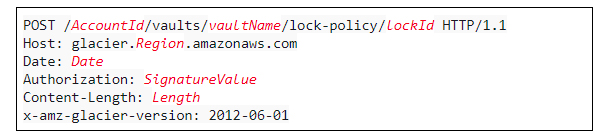
2. Use the lock ID to complete the locking process. Submit another POST request to the lock policy URI along with the lockID at the end. If you do not perform this step within 24 hours, the operation is automatically aborted. This gives you enough time to validate your vault lock policy.
If the POST request is successful, AWS returns an HTTP 204 response.
How To Abort Your Vault Lock Operation
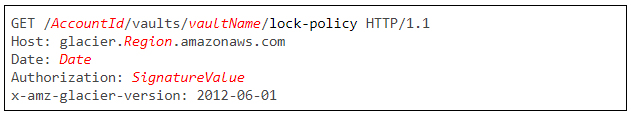
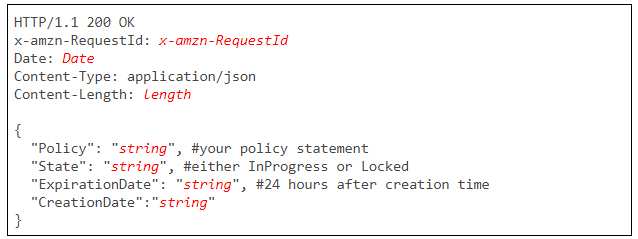
To know the state of your lock policy, whether it is still InProgress or already Locked, you can use send a GET request to your lock policy URI.
If your GET request is successful, AWS returns an HTTP 200 response:
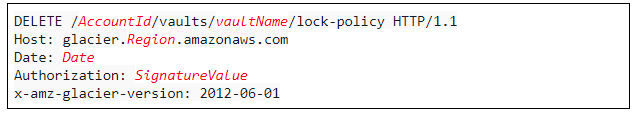
If your policy is still in an InProgress state, you can abort your lock policy operation and restart from the beginning.
If the abort operation is successful, AWS returns an HTTP 204 response.
Note: If you are studying for the AWS Certified Security Specialty exam, we highly recommend that you take our AWS Certified Security – Specialty Practice Exams and read our Security Specialty exam study guide.
Sources:
https://docs.aws.amazon.com/amazonglacier/latest/dev/vault-lock-how-to-api.html
https://docs.aws.amazon.com/amazonglacier/latest/dev/vault-operations.html
https://docs.aws.amazon.com/amazonglacier/latest/dev/vault-lock-policy.html