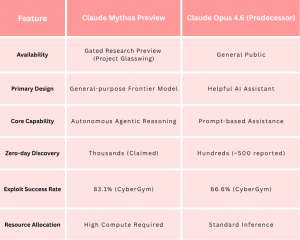
The announcement of Claude Mythos stirred the community towards the advancement of large language models and their application within the domain of cybersecurity. For more than two decades, the investigation and discovery of zero-day vulnerabilities have rested upon cybersecurity teams and researchers. However, the announcement of Claude Mythos, by Anthropic is claimed to be capable of autonomously identifying and weaponizing these security vulnerabilities at scale, This signals a potential shift in balance between offensive and defensive cyber capabilities. Ironically, it was reportedly discovered accidentally through Anthropic’s Content Management System. Unlike the publicly accessible version of Claude, Mythos remains restricted to internal testing in a gated preview from a pre-approved list within Anthropic. It is distinguished from its predecessors by its ability to perform the complex and iterative actions of a security researcher. This autonomy is enabled by an agentic workflow, wherein the model can interact with various software and tools while simultaneously using tool calling to validate hypotheses. In recognition of the model’s potential for dual use, Anthropic established Project Glasswing. This consortium reportedly brings together over 40 organizations, from cloud providers and cybersecurity firms to open-source foundations, to utilize Mythos for proactive hardening of vital internet infrastructure . This speed of vulnerability discovery suggests a shift in cybersecurity research. While Anthropic claims that human teams may take months to find and weaponize a high-impact zero-day vulnerability, Mythos is suggested to reduce this timeline to hours or days under certain conditions . Although the claims sound concerning, an increasing number of experts across technology and cybersecurity communities point to a disconnect between the reported zero-day findings and those that can actually be independently confirmed . As a result, some critics argue that Anthropic may be overstating its discoveries to build hype and maintain its visibility and influence. For instance, some reports suggest that Mythos operates through thousands of parallel sessions to uncover vulnerabilities in targets such as the Linux kernel and FFmpeg. Rather than relying purely on single-shot agentic prompting . In other words, autonomy exists yes, but it is amplified, and heavily compute-dependent. The primary justification for the restriction is the risk of misuse. Anthropic argues that a model capable of finding and patching vulnerabilities “at scale” could just as easily be used for exploitation. There are also reports from internal evaluations suggesting instances of “unsafe behavior,” including Mythos’ attempts to obscure reasoning or bypass constraints within testing environments . While these claims are not fully verified publicly, they contribute to the broader caution around release. Beyond safety, there is a clearer strategic layer. By limiting access to members of Project Glasswing, Anthropic effectively grants a strategic advantage to a select group of partners, allowing them to harden systems ahead of broader exposure. This creates a concentration of capability, one that begins to shift cybersecurity power dynamics toward large organizations with early access, while smaller firms, independent researchers, and open-source communities remain outside that boundary. Left to fend for themselves. The announcement of Claude Mythos has divided the tech and cybersecurity community into two camps: those who see it as a meaningful security assistant and those who interpret it as a calculated marketing scheme. Voices from major technology firms, argue that models like Mythos represent a path toward scaling cybersecurity beyond human limitations . Companies within Project Glasswing are testing Mythos from their security operations. Cloud platforms such as AWS and Microsoft, banks such as JPMorgan, and The Linux foundation are using it to identify and fix vulnerabilities at scale. Skeptics compared this moment to earlier events in AI model release, such as the staged release narrative around OpenAI’s GPT-2, where the restricted access amplified its perceived capability . The concern here is not that Mythos lacks capability, but that its presentation may blur the line between genuine advancement and marketing or even puffery. A more subtle but critical tension lies in private corporate control and state interests. Reports of friction between Anthropic and U.S. defense entities demonstrates the issue clearly: who ultimately controls systems capable of discovering and exploiting vulnerabilities at scale? The debate over the use of such models in military or surveillance suggests that frontier AI systems are no longer just technical and business assets, but also geopolitical. In scenarios where governments seek broader access while corporations impose restrictions, the balance of power becomes contested. Steps such as limiting access through initiatives similar to Project Glasswing may be framed as safety, but it also centralizes influence. In effect, a small cluster of corporations and aligned partners gain early defensive advantage, while states and especially smaller nations or independent actors may find themselves negotiating access rather than owning capability. Let’s look at this in two perspective: what is claimed, and what can be reasonably evaluated. The most credible aspect of the Mythos accidental announcement lies in performance signals. Reported benchmark improvements, such as high scores on SWE-bench and CyberGym, indicate that these systems are approaching a threshold where they can reliably assist in structured coding and security related tasks. Additionally, documented findings in projects like OpenBSD and FFmpeg suggest that AI systems, when paired with sufficient compute and tooling, can identify high impact software flaws . On the other hand, claims of “thousands of zero days” should be treated with caution. Some analyses indicate that observed results rely heavily on large-scale parallel execution rather than singular, fully autonomous reasoning . This does not negate the capability the system is powerful, but its strength lies in scale and iteration, not magic. What feels clear, at least for now, is this: these systems can find bugs, document them, and assist in remediation workflows. But the processes of validation, prioritization, and real-world patching remain deeply human. Rather than focusing purely on Mythos itself, it may be more useful that we look at what it represents. There is a visible trajectory toward integrating AI into the core of cybersecurity workflows. Not as a replacement, but as a force multiplier. But it is unlikely to be the silver bullet that both advocates and critics frame it as. Instead, it shows the shift in how security work is conducted, where human expertise is increasingly augmented by systems capable of persistent, large-scale analysis. AI-driven vulnerability assessment is not a distant concept as it is gradually becoming part of the standard toolkit in modern software development. Claude Mythos appears to be a real and meaningful development, but one that is still surrounded by a mix of verified progress and amplified expectations. The pace of advancement in AI-driven cybersecurity is accelerating, and the window between vulnerability discovery and exploitation is narrowing. What comes next is less about a single model and more about an emerging reality where both human and non-human actors will increasingly participate in the discovery of software flaws. The question is no longer whether this shift will happen but who gets access, and who gets left behind. Sources: https://www-cdn.anthropic.com/08ab9158070959f88f296514c21b7facce6f52bc.pdf https://www.anthropic.com/glasswing
Why Is Claude Mythos Getting So Much Attention?
Why You Can’t Access Claude Mythos
Industry Reactions: Breakthrough or Marketing?
Supporters: Generational Leap in Capability
Skeptics: Just Another GPT-2 Playbook
The Political & Socioeconomic Implications
So… Breakthrough or Hype?
Conclusion
Claude Mythos Explained, is it an AI Breakthrough or Overhyped Cybersecurity Threat?
AWS, Azure, and GCP Certifications are consistently among the top-paying IT certifications in the world, considering that most companies have now shifted to the cloud. Earn over $150,000 per year with an AWS, Azure, or GCP certification!
Follow us on LinkedIn, YouTube, Facebook, or join our Slack study group. More importantly, answer as many practice exams as you can to help increase your chances of passing your certification exams on your first try!
View Our AWS, Azure, and GCP Exam Reviewers Check out our FREE coursesOur Community
~98%
passing rate
Around 95-98% of our students pass the AWS Certification exams after training with our courses.
200k+
students
Over 200k enrollees choose Tutorials Dojo in preparing for their AWS Certification exams.
~4.8
ratings
Our courses are highly rated by our enrollees from all over the world.