Today, whenever someone hears you work in cybersecurity, especially in Vulnerability Assessment and Penetration Testing (VAPT), people often react like, “Ooh! Hacker!” then suddenly, “Can you hack my ex’s facebook?” or “hack our neighbor’s wifi for free internet connection.” Funny to hear, but this is where the misunderstanding starts. Many beginners jump into VAPT because it sounds cool, thinking it’s all about hacking anything you want without knowing what the role really involves.
Here’s the bad news and the good news. The bad news: VAPT is not “hacking.” It’s a professional security job and it is more than just “hacking”. The good news: if you’re curious about how attacks happen and you want to learn the right way, VAPT is a great path and this article will show you what VAPT looks like so you can start smarter and safer.
The Biggest Myth: “VAPT = Hacking”
VAPT is a security process where you check systems for weaknesses and help an organization fix them before real attackers can abuse them.
Vulnerability Assessment (VA) = finding and listing security issues
Penetration Testing (PT) = safely trying to exploit selected vulnerabilities to prove what an attacker can actually do. For example, getting access to data or higher permissions.
The whole point is “Ethical + scoped” because VAPT is only valid when it’s authorized, controlled, and safe. You must have:
- written permission
- clear targets
- agreed limits
so you don’t break systems, expose private data, or cause downtime. This is what separates professional VAPT from illegal hacking: the goal is to improve security, not to harm or show off.
Tools Don’t Equate Skill in VAPT
Scanners find clues, not truth.
Tools are helpful in VAPT, but they don’t make you skilled by default. Scanners like:
- Prowler: an AWS-focused security posture/compliance tool.
- Scout Suite: a multi-cloud security auditing tool (commonly used for AWS, Azure, and GCP).
- Nmap: Network/port scanner for discovery and service detection.
- OWASP ZAP: Web proxy and web vulnerability scanner with manual features.
can quickly spot possible issues, but they often produce false positives, miss context, or misunderstand how the app really works. Think of them as a flashlight, they help you see, but they don’t solve the problem for you.
Real VAPT starts when you manually validate the findings. You confirm if the issue is truly exploitable, check the real impact, and gather clear proof without damaging anything. This is how you avoid reporting “noise” and instead deliver findings that developers can actually fix.
VAPT is Mostly About Thinking (…and Note-taking)
The Threat mindset: “How could this be abused?”
VAPT is not just clicking tools. It’s mostly thinking like an attacker. You look at a feature and ask, “How could this be abused?”
like:
“Can I access something I shouldn’t, change someone else’s data, or bypass a restriction?”
This mindset helps you spot real risks that scanners often miss.
You need to document everything like you’ll defend it in a meeting. A good note-taking is what turns a “maybe” into a solid finding.
Document your steps clearly: what you tested, what you expected, what happened, and what proof you collected (screenshots, requests, logs, timestamps).
Write it like you’ll explain it in a meeting, because someone will ask, “How did you find this?” and “How do we fix it?”
Clear notes make your results credible and easier to patch.
Beginners Confuse Impact VAPT with Drama
Beginners often think a “serious” vulnerability must look dramatic, like defacing a website or doing something flashy.
But in real VAPT, the most dangerous issues can look simple, like broken access control, where a normal user can view or edit someone else’s data just by changing an ID or URL. Small bugs become high risk when they expose private information, allow unauthorized actions, or give higher privileges.
Also, VAPT is not about showing off. Your job is to provide clear proof that a weakness is real, not to cause damage or chaos. That means using safe testing: only the minimum actions needed to confirm impact, avoiding data deletion, service disruption, or anything that could harm the system.
Proof > flex, always.
The Secret Job: Communication
Writing clear findings and practical fixes + Talking to devs without sounding like a villain
In VAPT, your report matters as much as the testing. A good finding is clear and complete: what the issue is, where it happens, how to reproduce it, proof that it’s real, and why it matters. The best reports also include practical fixes, not just “patch it,” like exact settings to change, safer configurations, or better access rules.
When talking to developers, the goal isn’t to blame them, it’s to help them ship safer code. Use a calm, respectful tone and focus on the risk and the solution, not the mistake. If you explain the issue in simple terms and offer realistic remediation steps, devs are more likely to trust you and fix it faster.
What “Good VAPT” looks like
Good VAPT follows a clear flow:
You start by agreeing on what systems are included, then test them carefully and collect solid proof like screenshots, logs, and exact steps to reproduce. After that, you explain the real impact in simple terms, rate the risk, and give practical fixes the team can actually apply.
The most underrated step is retest. Many reports look good on paper, but you only know security improved when you verify the fixes worked. A quick retest confirms the vulnerability is gone, nothing else broke, and the organization is truly safer, not just “patched” in theory.
Your First Smart Next Step in doing VAPT
Your first smart next step is to pick one area and learn it deeply. It could be
- Networks
- Web Application
- Android
- iOS
- Cloud
When you focus, you’ll understand the basics faster and you’ll spot patterns more easily instead of getting overwhelmed by everything at once. Choose the one that matches your goal, like web testing if you enjoy websites, or cloud if you’re curious about AWS security.
Next, practice legally using labs, CTF platforms, and intentionally vulnerable apps so you build skills without crossing boundaries. While practicing, writing writeups show that you understand the process, not just the tools, and they help you stand out when applying for roles.
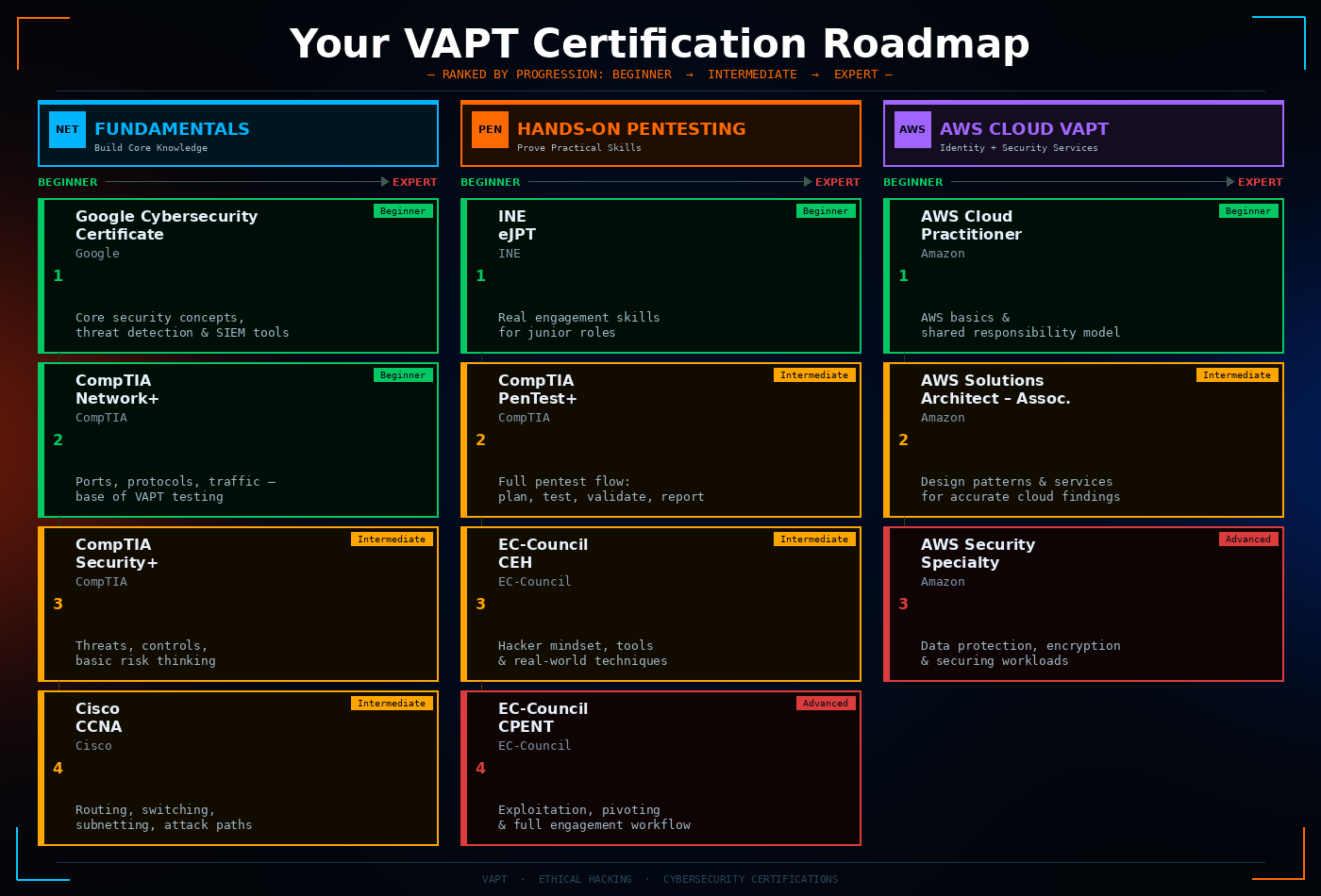
Certifications that Help (and what they’re actually for)
Beginner: build fundamentals (networking, security basics)
- Google Cybersecurity Certificate: Beginner-friendly program that introduces core security concepts like threat detection, network security, and SIEM tools.
- CompTIA Network+: helps you understand how networks work (ports, protocols, traffic), which is the base of most VAPT testing.
- CompTIA Security+: builds your core security foundation (threats, controls, basic risk thinking) before you go deeper into offensive testing.
- Cisco CCNA: strong networking foundation (routing, switching, subnetting, troubleshooting), which helps you understand real attack paths and network findings.
Hands-on: prove practical skills (labs, reporting mindset)
-
- INE eJPT: a beginner-friendly, hands-on pentesting cert that simulates real engagement skills for junior roles.
- CompTIA PenTest+: covers the full pentest flow (plan, test, validate, report) across common attack surfaces like web and cloud.
- EC-Council CEH: teaches how attackers think, covering real-world hacking tools, techniques, and methodologies used in penetration testing.
- EC-Council CPENT: designed to prove practical pentesting skills beyond beginner level, things like full engagement workflow, exploitation, pivoting, and reporting.
If you want AWS VAPT: identity + security services
- AWS Certified Cloud Practitioner: good starter to understand AWS basics and the shared responsibility model.
- AWS Certified Solutions Architect – Associate: helps you understand AWS design patterns and services, which makes your cloud findings more accurate and fixable.
- AWS Certified Security – Specialty: focuses on AWS security solutions (data protection, encryption, and securing workloads).
Conclusion
VAPT isn’t about hacking only, it’s a responsible security process where you find risks, prove what’s real, and help teams fix issues before attackers do. Through this, we cleared up the biggest myths of what makes a VAPT professional. If you’re serious about learning it the right way, start with one focus area, practice legally, and use certifications as a guide, not a shortcut.